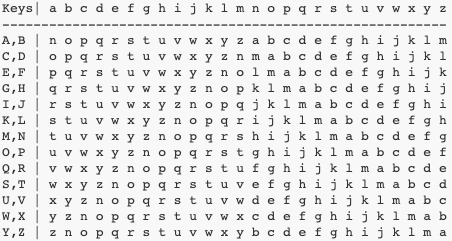
Exploring the Porta Cipher: A Comprehensive Guide, 2023, by Karthikeyan Nagaraj
Exploring the Porta Cipher: A Comprehensive Guide | 2023. Understanding the Features, Encryption Process, Decryption Process, and Use Cases of the Porta Cipher | Karthikeyan Nagaraj.

SSRF filter bypass. Hello, my name is W1C3 and today, I am…, by Josewice7
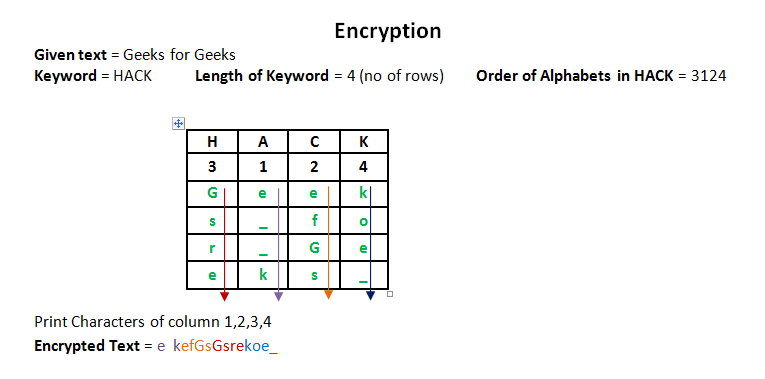
An Overview of Columnar Transposition Cipher: Features, Encryption, and Decryption, 2023, by Karthikeyan Nagaraj
Hacking JWT Tokens: Bruteforcing Weak Signing Key (JohnTheRipper), by Shivam Bathla

New Applications February 2021

PDF) Journal of Computer Science and Information Security November 2011 Mohammad Mazaheri, Funmeyo Ipeaiyeda, Bright Varsha, Md motiur rahman, Eugene C. Ezin, Journal of Computer Science IJCSIS, Jamaludin Ibrahim, and Shahram

Overview on security and privacy issues in wireless sensor networks-2014
Hacking JWT Tokens: jku Claim Misuse, by Shivam Bathla

PhysioBank, PhysioToolkit, and PhysioNet
OWASP Top 10: Cryptographic Failures, by Jeremiah Talamantes
How To Review Code For Vulnerabilities, by Vickie Li

IRJEdT - Journal with 599 Rs. publication fees, In 4 hr paper Low cost journal
Research Publications - St. George's University